ECDSA vs. RSA: Security, compatibility, and key size compared
Rivest-Shamir-Adleman (RSA) and Elliptic Curve Digital Signature Algorithm (ECDSA) underpin everyday security, including website authentication, app login verification, and software updates verified by digital signatures.
The choice between RSA and ECDSA depends on security strength, performance at scale, compatibility requirements, and key and signature overhead across Transport Layer Security (TLS), Secure Shell (SSH), and signing systems.
This guide compares RSA and ECDSA in terms of current use cases, security assumptions, equivalent security strength, and performance and resource usage on servers and devices.
Quick comparison of ECDSA vs. RSA
The table below summarizes key differences.
| RSA | ECDSA | |
| Common key sizes | 2048, 3072, and 4096-bit | 256- and 384-bit curves |
| Security strength mapping | 2048-bit RSA ≈ 112-bit 3072-bit RSA ≈ 128-bit |
224-bit ECDSA ≈ 112-bit 256-bit ECDSA ≈ 128-bit |
| Certificate size | Typically larger | Typically smaller |
| Signing efficiency | Typically less efficient | Typically more efficient |
| Verification efficiency | Typically more efficient | Typically less efficient |
| Adoption and compatibility | Broad support, including legacy environments | Broad support in modern systems, but legacy compatibility can be weaker |
| Compatibility fallback | Common fallback option | Requires client support |
| Quantum resistance | Not resistant to quantum attacks | Not resistant to quantum attacks |
What is RSA, and how does it work?
RSA is a public-key cryptography algorithm used for encryption and digital signatures. It uses a pair of related keys, but encryption and signing serve different purposes and use different standardized schemes:
- Public key: Used to encrypt data or verify signatures.
- Private key: Used to decrypt data or generate signatures.
An RSA public key consists of two values, written as (n, e): the modulus (n) and the public exponent (e). Together, they define the public-key operation used in RSA.
RSA operations use modular arithmetic (mod n), where calculations are performed within the arithmetic system defined by "n".
In practice, RSA uses standardized encryption and signature schemes that add padding and structure to the raw operations, making them secure.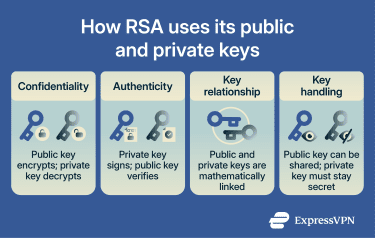
RSA keys and common key sizes
RSA keys are measured in bits, referring to the size of the modulus used in the algorithm. In certificate management systems, commonly supported key sizes include 2048, 3072, and 4096 bits.
2048-bit keys are still widely used in enterprise environments, while larger keys provide stronger protection but require more processing power.
RSA is also widely used in SSH for server and user authentication, where key sizes typically range from 2048 to 4096 bits. In modern SSH, RSA keys are typically used with SHA-256 or SHA-512 signature algorithms rather than the older SHA-1-based ssh-rsa signature mode.
While some legacy platforms support 1024-bit RSA keys imported from older systems, this is no longer recommended and isn't allowed for publicly trusted TLS server certificates.
Where RSA is used today
With its long history and broad compatibility, RSA works reliably across many client devices and legacy systems and is widely supported across cloud infrastructure and web services.
It’s commonly used in HTTPS/TLS, typically on port 443, including in application load balancers and content delivery networks (CDNs), where RSA certificates are often used for server authentication and digital signatures.
In some environments, certificate-based access management systems support only RSA, with 2048-bit keys commonly recommended.
RSA-based certificates are also widely used for software signing and verification in Windows environments.
RSA strengths and limitations
| RSA strength | RSA limitation | |
| Operational maturity | Established workflows support predictable rollout, renewal, and validation | Legacy workflows can be harder to modernize |
| Compatibility | Supports older clients and devices, reducing deployment friction | Compatibility requirements can slow the adoption of newer options |
| Key-size flexibility | Supports a wide range of key sizes to meet policy requirements | Larger keys increase processing and certificate overhead |
| Scalability impact | Widely used in production systems | Resource costs can rise at higher handshake or signing volumes, especially with larger keys |
| Deployment risk | Familiar tooling can reduce implementation risk | Retaining RSA for compatibility can add overhead compared with newer options |
What is ECDSA, and how does it work?
ECDSA is a public-key algorithm used for digital signatures. It uses a pair of keys: a private key to create the signature and a public key to verify it.
The signature is generated from a cryptographic hash of the message, a fixed-length fingerprint whose length depends on the hash function rather than the input size.
Each time ECDSA creates a signature, it must use a unique value, often denoted as “k.” This value plays a critical role in protecting the private key. If the same value is reused or generated poorly, the private key may be exposed.
To reduce this risk, deterministic ECDSA derives this value from the message and the private key instead of relying on fresh randomness during signing.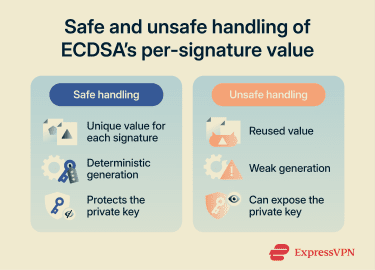
Common curves and key sizes
Instead of choosing any key length, ECDSA relies on predefined mathematical structures called named curves. These define the elliptic-curve parameters used by the algorithm, including how calculations are performed and the resulting security level.
Common examples include P-256, P-384, and P-521, also known as secp256r1, secp384r1, and secp521r1. The number refers to the approximate size of the curve’s underlying field in bits and is commonly used as shorthand for the curve size.
In SSH, ECDSA keys are commonly generated using 256-, 384-, or 521-bit curves. These correspond to the standardized National Institute of Standards and Technology (NIST) curves, which are also widely used in digital certificates, although naming conventions vary by protocol and implementation.
Where ECDSA is used today
ECDSA is widely supported in modern web infrastructure. Application load balancers, certificate management services, and CDNs support ECDSA certificates for HTTPS connections.
Many systems can present different certificates depending on what the client supports, allowing ECDSA and RSA to be used together for compatibility.
ECDSA is also supported in SSH through algorithms such as ecdsa-sha2-nistp256 and is used for server and user authentication.
ECDSA strengths and limitations
| ECDSA strength | ECDSA limitation | |
| Key size and efficiency | Smaller keys than RSA at comparable security levels | Efficiency depends on the curve, operation, and implementation |
| Standards support | Uses standardized named curves defined in public key standards | Interoperability depends on both sides supporting the same approved curves and algorithms |
| Compatibility | Supported by major platforms, certificate services, and SSH tools | Not all legacy clients support ECDSA |
| Signature generation | Deterministic variants work with standard verification | Poor handling of the per-signature value can expose the private key |
ECDSA vs. RSA: Detailed comparison
This section compares RSA and ECDSA across security assumptions, key sizes, performance, compatibility, and implementation complexity.
Security assumptions and attack surface
RSA and ECDSA are built on different mathematical problems:
- RSA’s security depends on the difficulty of factoring large integers.
- ECDSA relies on the difficulty of solving the elliptic-curve discrete logarithm problem.
Both are considered secure with approved parameters and sufficient key sizes. In practice, implementation and configuration choices are often a larger source of risk than the underlying mathematics.
For RSA, secure deployments depend on the correct use of standardized padding and signature schemes. Older schemes may remain in use for compatibility, but incorrect configuration can weaken an otherwise secure deployment.
ECDSA has a different risk profile. It depends on proper parameter handling and implementation. Poor randomness or side-channel weaknesses can undermine security.
Key size and equivalent security levels
RSA and ECDSA reach similar security levels using different key lengths. Elliptic curve keys achieve equivalent security with smaller key sizes. This doesn’t make RSA weaker, but it does mean RSA requires larger keys to provide the same level of resistance to attack.
Moving from 128-bit to 192-bit security, for example, increases RSA key sizes from 3072 bits to 7680 bits.
| Symmetric security level | RSA key size | ECDSA key size |
| 112-bit security | 2048-bit RSA | 224-bit ECDSA |
| 128-bit security | 3072-bit RSA | 256-bit ECDSA |
| 192-bit security | 7680-bit RSA | 384-bit ECDSA |
| 256-bit security | 15360-bit RSA | 521-bit ECDSA |
ECDSA uses smaller keys and signatures than RSA at comparable security levels. When selecting parameters, the key size, curve, and hash algorithm should be aligned in strength, since the overall protection is limited by the weakest component.
Performance and speed
Performance depends on which operation is measured and how the system is used. Signing, verification, handshake processing, and workload distribution can all affect real-world results. As a result, algorithm benchmarks do not always translate directly into deployment outcomes.
Resource usage on servers and devices
Key and certificate size directly affect bandwidth and storage. ECDSA certificates are typically smaller than comparable RSA certificates, which can reduce handshake size, bandwidth use, and storage requirements. This can be especially useful in constrained environments, such as Internet of Things (IoT) devices
RSA’s larger key sizes increase the sizes of certificates and signatures. In many environments, this overhead is manageable, but it becomes more noticeable at a larger scale.
Adoption and compatibility
RSA has a long deployment history and broad compatibility across legacy systems and older clients. ECDSA is widely supported in modern browsers, operating systems, cloud platforms, and certificate services. Both are supported in TLS 1.2 and TLS 1.3, although TLS 1.3 uses RSA for signatures rather than RSA key transport.
The remaining compatibility gap mostly affects outdated or unpatched systems. To address this, organizations often use ECDSA as the primary certificate and RSA as a fallback, allowing the server to select a certificate compatible with the client’s supported algorithms.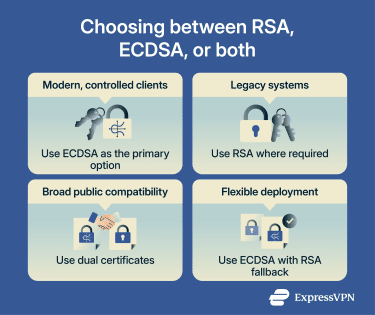
Implementation complexity and common pitfalls
Both RSA and ECDSA are safe when used through mature cryptographic libraries. Issues typically arise from implementation details rather than the algorithms themselves.
RSA: Implementation challenges
RSA implementations often use the Chinese Remainder Theorem (CRT) to speed up private-key operations. CRT stores additional mathematical values alongside the key to speed up these operations. This improves performance but increases sensitivity to faults, which can leak key information if not handled correctly.
Key generation is another common weak point. RSA keys depend on the secure generation of large prime numbers. Weak randomness or improper validation can produce weak keys.
ECDSA: Implementation challenges
ECDSA requires strict validation of public keys as points on the correct curve and subgroup. Skipping these checks can weaken security.
Signature encoding is another common source of issues. ECDSA signatures consist of two values (r and s) that must be encoded in a standard format so that different systems interpret them consistently.
In strict encoding formats, such as Distinguished Encoding Rules (DER), even small differences in a signature's format, such as extra leading zeros, can cause verification failures. Systems may also differ in how strictly they enforce these formatting rules.
Some ecosystems also enforce a “low-s” rule to prevent signature malleability (where one signature can be rewritten into another valid form). Inconsistent enforcement can lead to unexpected verification failures.
When to use ECDSA vs. RSA
Choosing between ECDSA and RSA isn’t about which algorithm is better in theory. It depends on where it runs, who needs to trust it, and how long it must remain in place without disruption.
For TLS certificates
If your traffic comes mostly from up-to-date browsers, mobile apps, and supported operating systems, ECDSA certificates are often preferred. They use smaller keys and signatures, which can reduce certificate and handshake overhead in environments such as CDNs and API gateways.
ECDSA works well in:
- Public-facing services targeting modern clients.
- High-traffic environments with large connection volumes.
- Latency-sensitive APIs and mobile-heavy workloads.
- Cloud-native stacks using automated certificate management.
If legacy clients must be supported, RSA is often the most broadly compatible fallback option, since some older or unpatched clients may not support ECDSA certificate deployments. Before removing RSA, verify compatibility across all client software and devices in use.
In practice, many services use both ECDSA and RSA certificates to balance efficiency and compatibility. Servers present an ECDSA certificate to clients that support it and fall back to RSA for older or incompatible clients.
| Context | Decision |
| Public internet service with unknown clients | Dual certificate (ECDSA + RSA) |
| Controlled internal service with managed clients | ECDSA-only when client support is verified |
| Highly regulated or legacy-heavy environment | RSA may be operationally simpler |
For SSH and authentication keys
For SSH access and user authentication, both RSA and ECDSA are widely supported, but the choice depends on the environment.
ECDSA is a suitable default in modern environments, particularly in:
- Modern servers and clients.
- Automated key rotation (automatic key replacement on a schedule).
- Shorter keys in configuration files and backups.
- Large-scale key provisioning (creating and distributing keys across many systems).
RSA remains useful in environments where compatibility or existing policies matter. For example, some older SSH clients don’t support elliptic-curve keys, and some environments still depend on RSA-based workflows or legacy tooling.
Also note that while RSA keys remain widely supported in SSH, older SHA-1-based ssh-rsa signatures are disabled by default in modern OpenSSH, so compatibility may depend on whether systems support the newer RSA/SHA-2 signature algorithms.
If the environment depends on these constraints, switching key types may require updating policies, tooling, or validation processes.
| Context | Decision |
| Modern fleet, cloud-native environment | ECDSA is a suitable default |
| Mixed-age infrastructure or strict legacy compliance requirements | Keep RSA available |
For code signing and documents
Code signing and document signing have different constraints than TLS or SSH. Here, platform requirements and ecosystem support often matter more than efficiency.
Many operating systems and software distribution platforms define which algorithms are accepted for signing software, such as applications, drivers, or update files.
In some ecosystems, these policies explicitly require RSA-based signing certificates. For example, some current Windows code-signing and policy-enforcement paths don't support Elliptic Curve Cryptography (ECC) signatures.
Beyond platform constraints, signature size and longevity can also influence the choice. In firmware distribution and constrained-device environments, smaller signatures can reduce update size and bandwidth usage when ECDSA is supported.
Another consideration is longevity. With trusted timestamping, a code signature may remain valid even after the signing certificate expires, depending on platform policy and validation rules. If long-term validation is required, confirm that validation systems support the chosen algorithm throughout its lifecycle.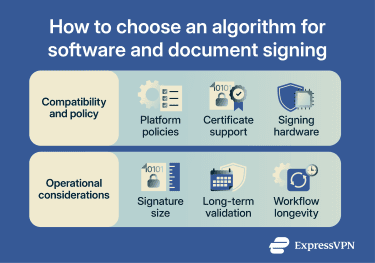
Best practices for secure implementation
The practices below focus on the specific configuration and operational decisions that affect whether RSA and ECDSA are secure in production:
- Modern RSA sizes and padding: Use at least 2048-bit RSA keys, and larger sizes where required by policy or security-strength goals. For signatures, prefer the RSA Signature Scheme with Appendix–Probabilistic Signature Scheme (RSASSA-PSS). For encryption, use RSA Optimal Asymmetric Encryption Padding (RSA-OAEP) instead of older padding formats.
- Approved curves and parameters: Use standardized named curves such as P-256 or P-384 rather than custom parameters. Match them with appropriate hash functions of compatible strength, such as Secure Hash Algorithm (SHA-256) or SHA-384, to maintain balanced security.
- Secure randomness and key storage: Generate keys using the operating system’s cryptographic random number generator. Store private keys in hardware-backed modules, where possible, such as Hardware Security Modules (HSMs), secure enclaves, Trusted Platform Module (TPM)-based keystores, or isolated cryptographic services, to reduce exposure in application memory.
- Strict verification and validation: Treat all signature and certificate inputs as untrusted. Use strict parsing, fully validate certificate chains, and fail securely on verification errors.
- Reduce timing and side-channel risks: Use hardened, constant-time implementations where available so execution behavior doesn’t reveal secrets. Keep libraries up to date and avoid exposing detailed cryptographic error information to external users.
The quantum threat and migration path
Large-scale quantum computers running Shor’s algorithm could compromise the mathematical foundations of both RSA and elliptic-curve cryptography by recovering private keys from public keys. This isn’t addressed by increasing key sizes, and switching between RSA and elliptic-curve cryptography doesn't reduce that exposure.
The risk is inherent to how these algorithms work, but practical quantum machines capable of doing this at scale don’t exist today. The main long-term concern is encrypted data captured today that could be decrypted in the future if quantum-capable adversaries emerge.
To address this, post-quantum cryptography is being standardized to resist known quantum attacks, and NIST has already published its first finalized post-quantum cryptography standards, including the Module-Lattice-Based Key-Encapsulation Mechanism (ML-KEM), the Module-Lattice-Based Digital Signature Algorithm (ML-DSA), and the Stateless Hash-Based Digital Signature Algorithm (SLH-DSA).
Most environments are likely to introduce these algorithms gradually through hybrid deployments that combine classical and post-quantum methods, rather than replacing everything at once. For example, ML-KEM can be added to key exchange while a classical method remains in place.
Organizations should identify where they rely on public-key cryptography, review vendor roadmaps, and ensure that future infrastructure supports a transition as standards and the ecosystem mature. In practice, this often means tracking emerging standardized algorithms, such as ML-KEM (formerly Kyber), as implementations and deployments evolve.
Also read: ExpressVPN launches post-quantum protection to defend against future threats.
FAQ: Common questions about ECDSA vs. RSA
Is RSA still secure today?
Is RSA used for encryption or signatures?
Does ECDSA encrypt data?
Is ECDSA faster than RSA?
What Elliptic Curve Digital Signature Algorithm (ECDSA) key size matches RSA 2048?
Can ECDSA keys expire?
How do I switch from RSA to Elliptic Curve Digital Signature Algorithm (ECDSA) certificates?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN