-
What are Google dorks? A complete guide to risks and safe use
Google is designed to help people find useful information. But with the right search operators, it can also pull up results that are harder to discover with a generic search, like certain login pages ...
-
What is threatware? A complete guide to risks and protection
Threatware is a catch-all term representing any malicious software or tool designed to harm, exploit, or compromise systems, data, or networks. It includes viruses, ransomware, spyware, Trojans, worms...
-
Nation-state cyber actors: Who they are and why they matter
Reporting on state-linked cyber operations is frequent and often high-stakes, yet the terminology, attribution, and strategic context can be difficult to interpret consistently. This article examines ...
-
What is cyber threat hunting, and how does it work?
A virus or malware that infects your system doesn’t always attack right away. Advanced and targeted threats can lie dormant, collecting data, searching for sensitive information, or stealing credent...
-
What makes polymorphic viruses so hard to detect?
Polymorphic viruses are designed to evade security tools while infecting devices, systems, and networks. The first step to avoiding these threats is understanding how they work, and this article provi...
-
What is a smurf attack and why is it a security risk?
A smurf attack is a denial-of-service (DoS) attack that can make systems or services unavailable without breaking into them or exploiting software flaws. Instead of targeting user accounts or applicat...
-
How to prevent a ping flood attack on your network
Not all network disruptions come from advanced malware or sophisticated hacking tools. Sometimes, everyday network behavior is simply pushed too far. A ping flood attack takes a basic connectivity che...
-
EternalBlue explained: What it is and how to stay safe
You may have heard of WannaCry and NotPetya, two ransomware outbreaks that caused widespread disruption around the world. What these attacks share in common is the use of an exploit called EternalBlue...
-
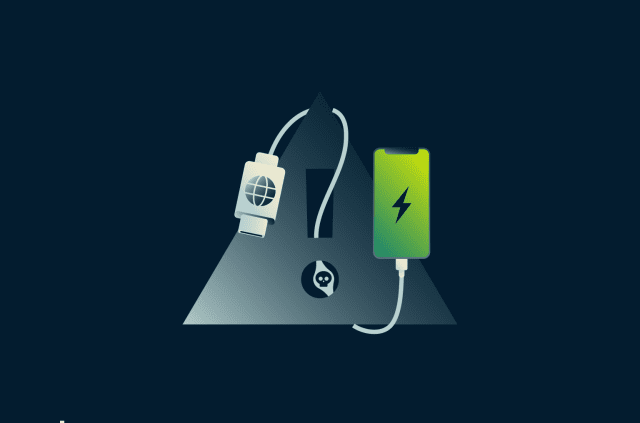
How to protect your phone from juice jacking attacks
It’s inevitable: phones need regular recharging, and sometimes that means topping up in public. Security researchers have shown that it's theoretically possible to compromise a phone through a proce...
-

DNS over QUIC (DoQ): Everything you need to know about the new DNS protocol
Almost everything you do online starts with looking something up using the Domain Name System (DNS). Often called the internet’s address book, DNS is how your device turns a website name, like www.e...

Don't miss the Spring Deal: Save up to 78% before April 21.
Don't miss the Spring Deal: Save up to 78% before April 21. Claim now!
Claim Now!

